Building an Enterprise Network with OPNsense: A Complete Stack Overview
On my BOTUM infrastructure, I replaced a commercial firewall with an OPNsense VM on Proxmox. Result: enterprise-grade security, fully under control, for under $300 in hardware. Here's the complete architecture — and the detailed guides for each component.
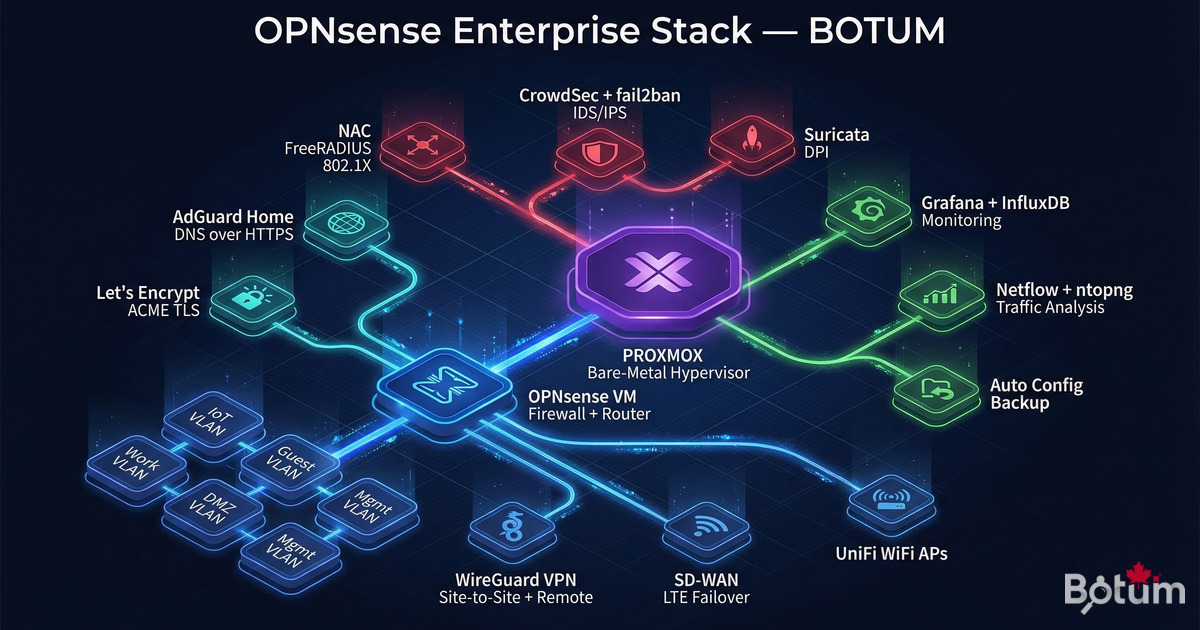
On my BOTUM infrastructure, I replaced a commercial firewall with an OPNsense VM running on Proxmox. Enterprise-grade security, fully self-hosted, for under $300 in hardware. This series documents every component of the stack.
Posts in This Series
- Post 1 — Install OPNsense in Proxmox: Complete Step-by-Step Guide
- Post 2 — Zero Trust VLANs: Isolating IoT, Work, Guest and DMZ (coming soon)
- Post 3 — WireGuard VPN: Site-to-site + Remote Workers (coming soon)
- Post 4 — WiFi by VLAN: APs and Segmented SSIDs (coming soon)
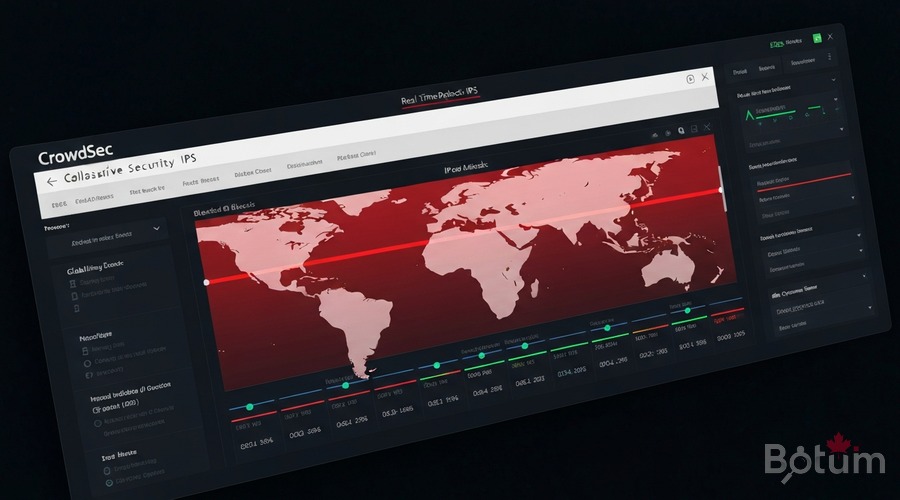
- Post 5 — CrowdSec + fail2ban: Collaborative IDS/IPS (coming soon)
- Post 6 — SD-WAN with Automatic LTE Failover (coming soon)
- Article 6 — NAC with FreeRADIUS & 802.1X: Network Access Control
- Article 7 — Suricata IDS/IPS: Intrusion Detection and Deep Packet Inspection
- Article 8 — AdGuard Home + DNS over HTTPS: DNS Filtering and Privacy
- Article 9 — OPNsense Monitoring with Grafana and InfluxDB: Real-Time Dashboards
- Article 10 — CARP & High Availability: Active/Passive OPNsense Pair
- Article 11 — Lightweight SIEM with Wazuh: Centralize and Correlate All Stack Logs
- Article 12 — Ansible as Code for OPNsense: Deploy and Version Your Infrastructure in One Command
- Article 13 — Automated OPNsense Config Backup
- Article 14 — Let's Encrypt Certificates with ACME on OPNsense
- Article 15 — NetFlow + ntopng — Network Traffic Analysis
Why OPNsense Over pfSense?
Stack Architecture
Proxmox (bare-metal hypervisor)
└── OPNsense VM (firewall + router)
├── WireGuard → Site-to-site VPN + remote workers
├── WiFi → APs + SSID per VLAN (IoT/Work/Guest)
├── SD-WAN → Automatic LTE failover
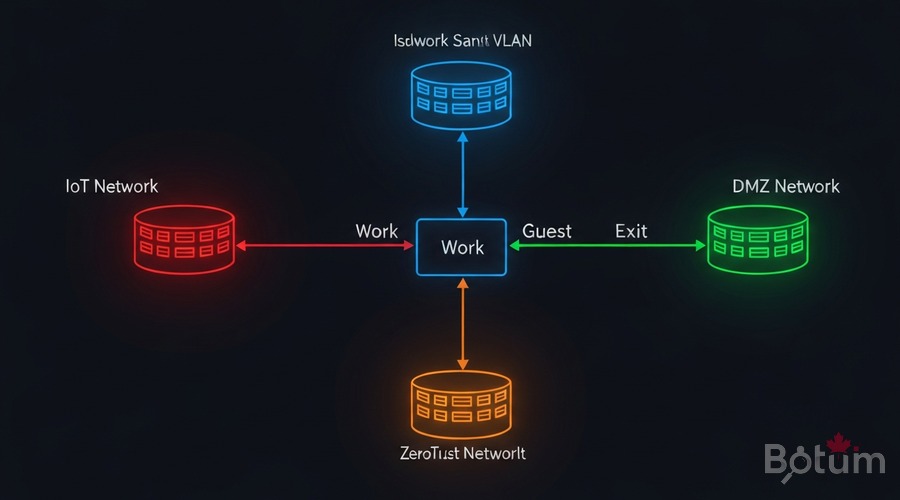
├── VLANs → IoT / Management / Production / DMZ
├── Zero Trust → Inter-VLAN rules
├── CrowdSec → Collaborative IDS/IPS
└── fail2ban → SSH protectionComponent Overview
VLANs — Zero Trust Segmentation
WireGuard — VPN
Natively integrated since OPNsense 21.7. Site-to-site + remote access. Latency < 5ms.

CrowdSec — Collaborative IDS/IPS
~300 new blocking decisions per day on my BOTUM infrastructure. Automatically.
Where to Start?
→ Install OPNsense in Proxmox — Complete Guide
Téléchargez ce guide en PDF pour le consulter hors ligne.
⬇ Télécharger le guide (PDF)Series Articles
🚀 Aller plus loin avec BOTUM
Ce guide couvre les bases. En production, chaque environnement a ses spécificités. Les équipes BOTUM accompagnent les organisations dans le déploiement, la configuration avancée et la sécurisation de leur infrastructure. Si vous avez un projet, parlons-en.
Discuter de votre projet →
